- Data Privacy Day commemorates the Jan 28,1981 signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection.
- Millions of us still don’t fully understand how our personal information is being used, collected and shared.
- Allwork.Space caught up with John Gilmore, DeleteMe’s Head of Research, to find out more about some of the data privacy challenges facing consumers and businesses today.
January 28 is Data Privacy Day. But don’t worry if you’re reading this a few days, weeks or even months later – the content of this article could still prove useful.
Data Privacy Day commemorates the Jan 28,1981 signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection.
Millions of us still don’t fully understand how our personal information is being used, collected and shared. Data Privacy Day aims to raise awareness and educate both individuals and businesses on privacy and data protection best practises.
Earlier this month, DeleteMe, a company that facilitates the removal of people’s personal information from the internet, released its 2021 PII Marketplace Report.
The report highlights the metrics, trends, consumer behaviours and attitudes shaping the ecosystem of online personal information.
Allwork.Space caught up with John Gilmore, DeleteMe’s Head of Research, to find out more about some of the challenges facing consumers and businesses today.
DeleteMe, which was founded in 2011, removes personal identifiable information (PII) from data broker operations and people search websites. These are the two main places an organisation would go to to find personal data on people, explains Gilmore.
As it stands, the global data broker ecosystem is a $200bn industry. There are more than 4,000 data brokers worldwide, with hundreds of data points for every person who has ever spent any time on the internet.
People search websites “are like online directories and they’re completely unregulated”, Gilmore adds. They contain a wealth of PII on individuals, from their phone number and address to which school they went to and relatives’ names.
Without regulation in place, removing PII from the internet isn’t always easy, and it’s actually impossible to permanently remove it (as we’ll find out later).
Our PII is everywhere
Gilmore acknowledges that while a lot of people search websites and data broker companies operate voluntary policies on removing information on request, not all of them do.
“On one hand we’re sending out cease and desist letters to a lot of these operations, and when they receive them, as long as they’re validated as representing the individual, they will take the information down.”
Regulation is beginning to catch up in some parts of the world, such as in Europe, where the EU introduced GDPR in 2018. To summarise, GDPR is a set of rules designed to give EU citizens more control over their personal data.
“If you send a GDPR request you will get it removed. Different states in the US are now passing new privacy regulations and businesses will be forced to comply, whereas in the past it’s really just been about making them honour their own user agreements.”
In the process of getting people’s data removed, DeleteMe tracks and analyses how people’s PII is being used and publishes its findings in its annual report.
“In the last couple of years we’ve noticed that the level of detail of information that was available for the people who came and used our service was growing.”
Gilmore attributes this rise in available PII to the fact that most of us have been spending more time online during the pandemic, including in a remote working context. Many of us are also using more online communication platforms now than we did before Covid-19.
Although the amount of PII available online has doubled, the important thing to note is that the information itself has become more detailed, says Gilmore.
“It used to be that the most commonly available stuff was what you’d think of as directory-level information: name, phone number and address.”
“You could pretty much send everyone in the world junk mail if you wanted to, but you couldn’t necessarily get their work email address or be able to accurately identify the names of their children. What we’ve found is that higher levels of detail have now become the norm.”
“If you want to get information on someone, instead of it taking you 30 minutes to get a very detailed profile of someone, it’ll take you five minutes,” says Gilmore.
Fraud is on the rise
PII availability has led to a significant increase in identity theft and fraud.
Gilmore says that although around half of fraud over the two years was “due to laxer policy to ensure [Covid-19] benefits spending got out the door,” the other half is a consequence of more people being engaged in remote-work.
According to Gilmore, there are two main types of online fraud, or rather two ways to go about it. The first is “fishing.” This is when a fraudster automates emails, phone calls and texts to essentially “blanket the planet with fraudulent outreach.”
The second is known as spear phishing, and it’s when more detailed PII is leveraged. “Where PII typically comes into play isn’t in the outreach, it’s in the exploit,” adds Gilmore.
An example of spear fishing would be when the victim “presses one for more information” on a fraudulent phone call, at which point a human being poses as representative of the company or organisation they’re trying to impersonate.
They might say something like “we see you’ve got an account with us” starting on a specific date, or will recite another piece of information about the victim to make the call sound more credible. These scammers collect PII from different sources.
“It’s not like everybody works off one set of data. What usually happens is that when they design the scam, they say ‘here are the kinds of pieces of information we would like to use that make it compelling,’ and they actually A/B test them to see [which is most effective].”
When it comes to scams, one of the most successful pieces of PII is the names of people’s relatives, says Gilmore. It’s an intimate detail that lures victims into a false sense of security.
Scammers might allude to a family member, i.e. by asking the victim “is your wife’s name Helen?” Others might impersonate a family member and persuade the victim to click on a link.
The number of businesses and other organisations experiencing ransomware attacks has also doubled, with scammers using “the exact same ingredients and techniques”.
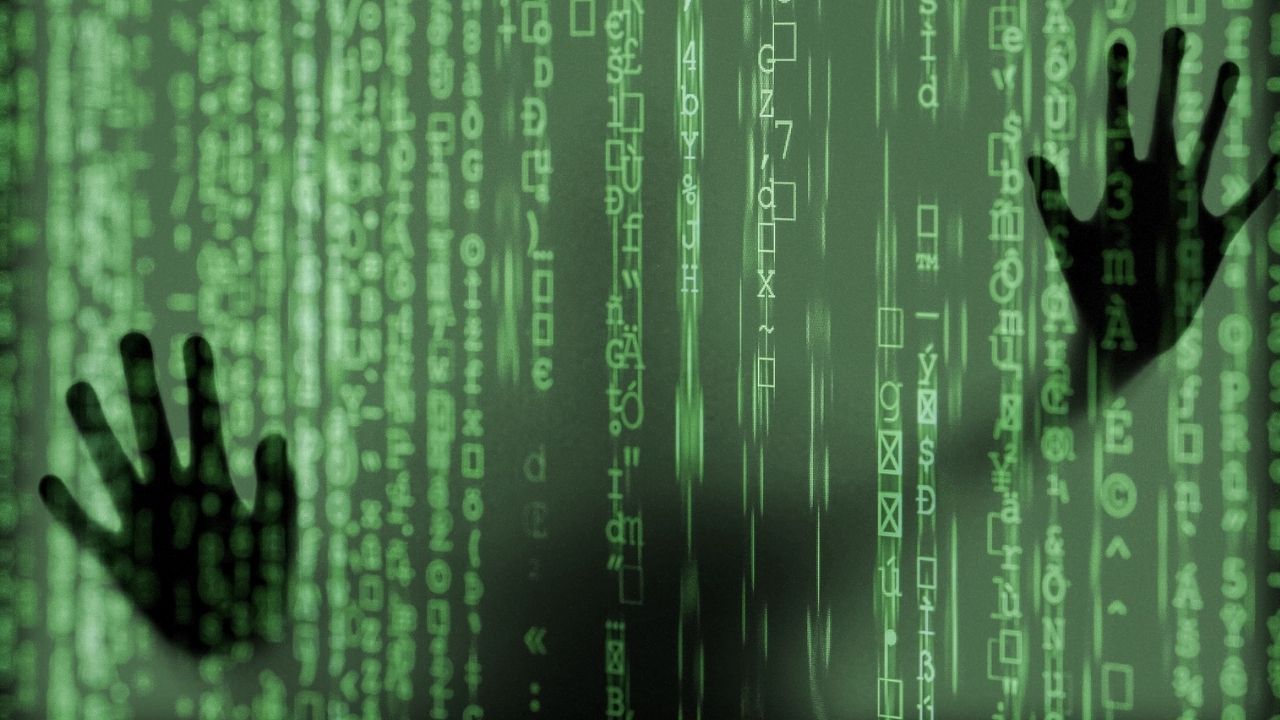
We used to think of cyber attacks as being orchestrated by a guy in a hoodie who’d sit in front of computer screens and figure out a way to break through an organisation’s network passwords, but that’s not how it works in reality, says Gilmore.
A business’ network is more likely to be penetrated because an employee has opened a scam email and clicked on a link that’s connected to a piece of malware.
Is PII protection the new “work perk?”
DeleteMe sells privacy services to businesses as well as individuals.
“It was interesting,” says Gilmore. “When we were approaching businesses we didn’t fully grasp what their use case would be – why would they want to remove their workforce’s PII?”
The media
The first organisations to approach DeleteMe were involved in the media, including the New York Times, Buzzfeed, Vox, and Gannett, a local newspaper network in the US.
“They said this is vital for us because all our journalists are putting their names out there on the internet and they’re either at risk from stalking and harassment because of the stories they write, or because they’re easy to spoof.”
A scammer could assume a journalist’s identity and send emails designed to infiltrate an organisations’ network using ransomware, for example.
Tech companies
“Then there were a lot of high tech companies in California who were aware of personal information abuse – that was the second group of companies that started working with us.
“Some companies want to protect the reputation of employees, while others see it as organisational protection: we’re reducing our exposure to potential cyber attacks.”
Public sector
More recently, public sector organisations have been subscribing to DeleteMe’s service. “If you look at the targets of cyber attacks from the last three years, you’ll see that there’s been this big boom in healthcare and government.
“Most of these organisations are transparent by design…they’re essentially the low-hanging fruit of the digital world.” Some governments are taking steps to make their online systems more secure. The US recently approved over $500 million in cybersecurity funding.
IPOs
A dozen companies over the last two years have used DeleteMe’s business service as part of their strategy to safeguard their IPO.
“There are competitors who don’t want a company to go public or there are people who have a financial interest in the IPO failing. Key people in these companies may be targeted and their reputation attacked on places like bulletin boards for stock traders
“So, they’ve said we want to protect all of our employees until the IPO is complete, because we see it as risk protection. And it’s very cheap risk protection.”
PII protection can also be offered as a work perk alongside retirement plans, etc.
“If you’re hiring people who live hundreds of miles away from your office, the company is saying we understand that you’re going to be on the internet all the time; we’re going to make sure we provide you with protection while you’re living in cyberspace.”
Can PII really be deleted?
Nobody’s PII is ever permanently deleted from the internet, it’s just made harder to get. Gilmore likens the removal process to a game of whac-a-mole.
“You temporarily remove things from certain places, but you can never stop the flow of information. Even if you remove all of someone’s information from public sources today, six months from now, most of it will be there again.”
“Most of the sources that feed into public data brokers and people search sites automate the collection of information. They write scripts that farm information from public records – they have bots that will scrape sources from public places and social media.”
So, if you have a Facebook page, someone is scraping it and it’s popping up on a variety of databases as you’re reading this article.
“Companies in the tech industry understand this sometimes in ways that others don’t. When we say we say: we can’t permanently remove information, we can make it harder to get, they go: that’s fine, that’s exactly what we want.”
Although complete online privacy is impossible, it’s still worth taking steps to enhance it. Let’s say a scammer is presented with two companies: A and B.
They’ve managed to source seven data points on every employee in company A, and three data points of every employee in company B.
“They’re going to go after company A because the chances of them having a successful ransomware attack is much higher with the company that we have more data on.”
“Fragmenting data and making it harder to get interrupts the processes that fraud perpetrators use. It makes their jobs more difficult – and they don’t like difficult!”
Changing mindsets
If you run a business and want to protect your employees’ privacy as much as possible, “don’t collect information you don’t need,” says Gilmore. This is known as privacy by design.
“Instead of trying to encrypt information and make it harder to exploit, assume that everything in your company is going to be stolen.”
Business owners should take some time to reflect on their online processes – including how they collect information and store it, and how employees communicate with each other.
When it comes to data privacy, workplace culture is changing. Gilmore works with companies whose employees don’t interact on online channels using profile pictures or their full name, for instance.
Others have decided to ditch email signatures for the purposes of data privacy, and use temporary email addresses to communicate with companies they are yet to build a relationship (and level of trust) with.
“I don’t use my personal phone for business, I use a Google account that has no connection to me. It’s just an artificial number and if anyone starts spamming it I can create a new one – it doesn’t matter. If my personal phone gets compromised it’s more of a problem,” Gilmore said.
To find out more about how to keep your data safe, visit staysafeonline.org.